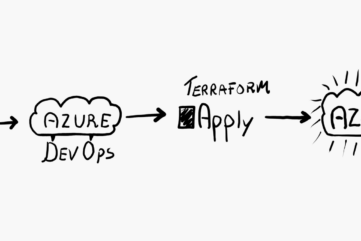
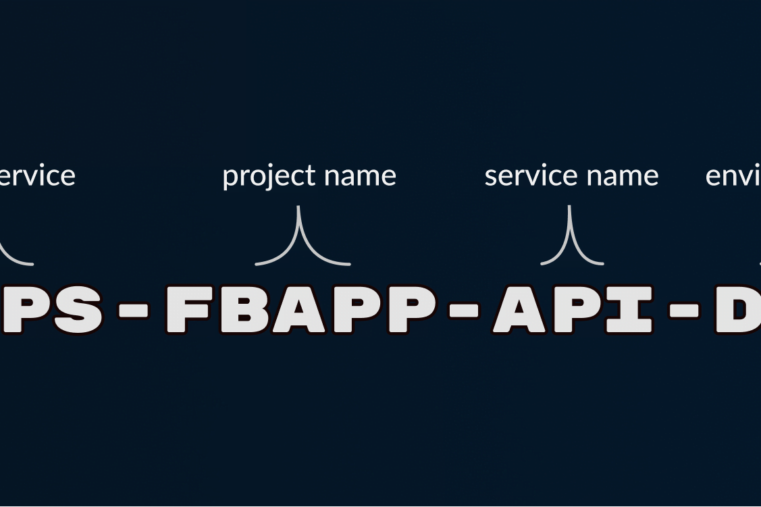
By having prefixes and a structure by type, project name, and environment, it will be faster for your eyes to spot resources and easier to remember. It also works great with IaC....
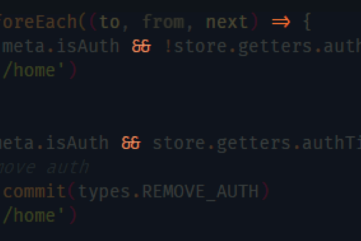
Sweet ligatures. They make the code more expressive and easier to read....
I have decided to start a blog focused on developer stuff and...